TLS/SSL handshake processing
In this documentation, the term TLS/SSL handshake represents the two-way handshake that initiates encrypted sessions in both the SSL protocol and its successor protocol, TLS.
In an inline deployment, the system processes the TLS/SSL handshake, potentially modifying the ClientHello message and acting as a TCP proxy server for the session.
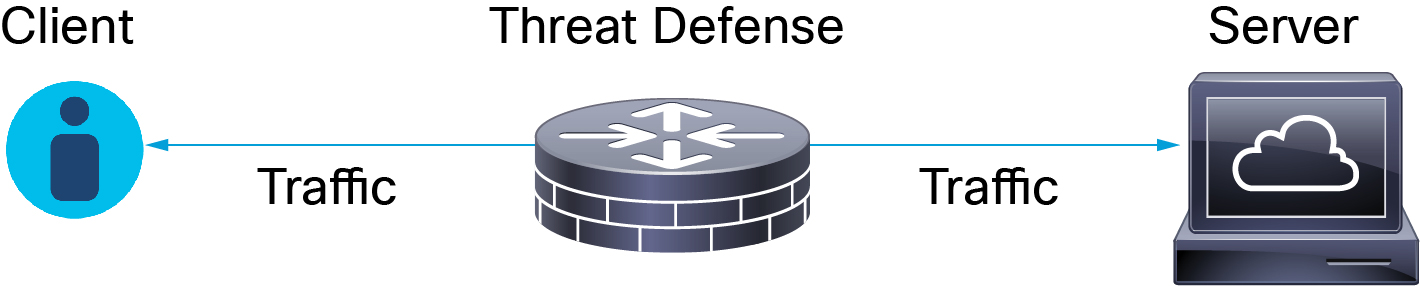
The following figure shows an inline deployment.
After the client establishes a TCP connection with the server (after it successfully completes the TCP three-way handshake), the managed device monitors the TCP session for any attempt to initiate an encrypted session. The TLS/SSL handshake establishes an encrypted session using the exchange of specialized packets between client and server. In the SSL and TLS protocols, these specialized packets are called handshake messages. The handshake messages communicate which encryption attributes both the client and server support:
-
ClientHello—The client specifies multiple supported values for each encryption attribute.
-
ServerHello—The server specifies a single supported value for each encryption attribute, and the ServerHello response determines which encryption method the system uses during the secure session.
After a TLS/SSL handshake completes, the managed device caches encrypted session data, which allows session resumption without requiring the full handshake. The managed device also caches server certificate data, which allows faster handshake processing in subsequent sessions that use the same certificate.