IAB logging and analysis
IAB logging and analysis is a monitoring system that
forces an end-of-connection event. This event logs both bypassed flows and flows that would have been bypassed, regardless of whether you have enabled connection logging
provides connection events. These events indicate when flows are bypassed in bypass mode or would have been bypassed in test mode, and
enables custom dashboard widgets and reports based on connection events. These widgets and reports display long-term statistics for bypassed and would-have-bypassed flows.
IAB connection events
IAB connection events provide specific information about bypassed and would-have-bypassed flows through these key fields:
Action: When Reason includes
Intelligent App Bypass:-
Allow—indicates that the applied IAB configuration was in test mode and traffic for the application specified by Application Protocol remains available for inspection.
-
Trust—indicates that the applied IAB configuration was in bypass mode and traffic for the application specified by Application Protocol has been trusted to traverse the network without further inspection.
-
Reason:
Intelligent App Bypassindicates that IAB triggered the event in bypass or test mode.Application Protocol: This field displays the application protocol that triggered the event.
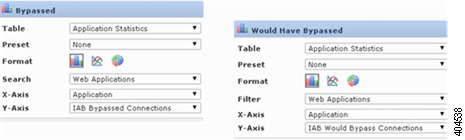
You can create custom analysis dashboard widgets to display long-term IAB statistics based on connection events. Specify these settings when creating the widget:
Preset: None
Table: Application Statistics
Field: any
- Aggregate: either of:
IAB Bypassed Connections
IAB Would Bypass Connections
Filter: any
You can create custom reports to display long-term IAB statistics based on connection events. Specify these settings when creating the report:
Table: Application Statistics
Preset: None
Filter: any
X-Axis: any
- Y-Axis: either of:
IAB Bypassed Connections
IAB Would Bypass Connections
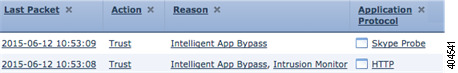
Connection event examples
In the truncated graphic, some fields are omitted. The graphic shows the Action, Reason, and Application Protocol fields for two connection events resulting from different IAB settings in two separate access control policies.
For the first event, the Trust action indicates that IAB was enabled in bypass mode and Bonjour protocol traffic was trusted to pass without further inspection.
For the second event, the Allow action indicates that IAB was enabled in test mode, so Ubuntu Update Manager traffic was subject to further inspection but would have been bypassed if IAB had been in bypass mode.

In the truncated graphic, some fields are omitted. The flow in the second event was both bypassed (Action: Trust; Reason: Intelligent App Bypass) and inspected by an intrusion rule (Reason: Intrusion Monitor). The Intrusion Monitor reason indicates that an intrusion rule set to Generate Events detected but did not block an exploit during the connection. In the example, this happened before the application was detected. After the application was detected, IAB recognized the application as bypassable and trusted the flow.
In the custom analysis dashboard widget examples:
The Bypassed example shows statistics for application traffic bypassed because the applications were specified as bypassable and IAB was enabled in bypass mode in the deployed access control policy.
The Would Have Bypassed example shows statistics for application traffic that would have been bypassed because the applications were specified as bypassable and IAB was enabled in test mode in the deployed access control policy.
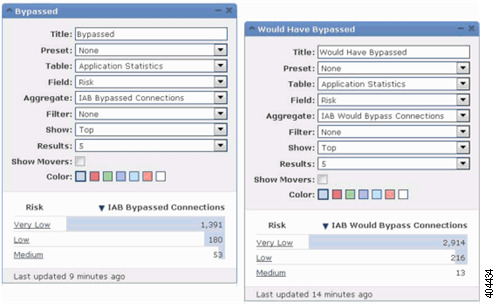
The graphic shows two abbreviated report examples:
The Bypassed example shows statistics for application traffic bypassed because the applications were specified as bypassable and IAB was enabled in bypass mode in the deployed access control policy.
The Would Have Bypassed example shows statistics for application traffic that would have been bypassed because the applications were specified as bypassable and IAB was enabled in test mode in the deployed access control policy.