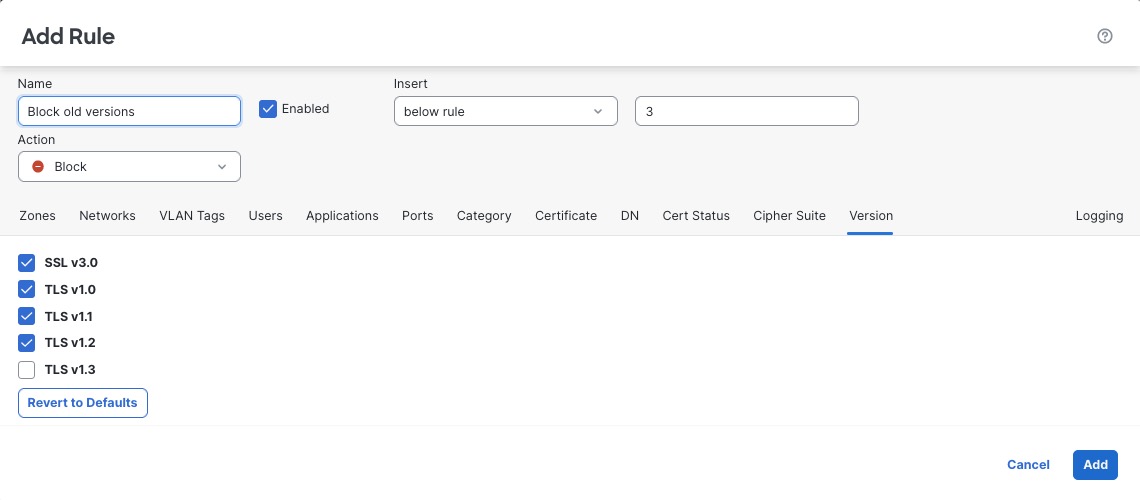
Encryption protocol version rule conditions
You can choose to match against traffic encrypted with SSL version 3.0, or TLS version 1.0, 1.1, or 1.2. By default, all protocol versions are selected when you create a rule; if you select multiple versions, encrypted traffic that matches any of the selected versions matches the rule. You must select at least one protocol version when saving the rule condition.
You can use SSL 3.0 in a Do Not Decrypt, Block, or Block with Reset rule action.
You cannot select SSL v2.0 in a version rule condition; the system does not support decrypting traffic encrypted with SSL version 2.0. You can configure an undecryptable action to allow or block this traffic without further inspection. For more information, see Set default handling for undecryptable traffic.
Important | Protocol version rule conditions should be used only to block traffic, they should not be used to decrypt traffic. |