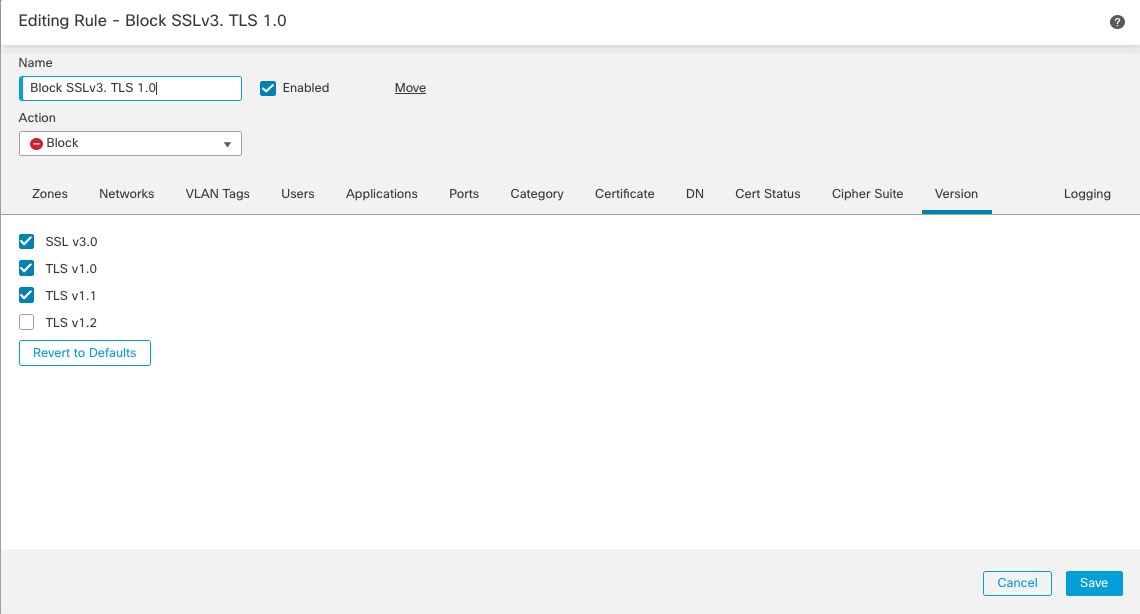
Example: Decryption Rule to Monitor or Block Protocol Versions
This example shows how to block TLS and SSL protocols on your network that are no longer considered secure, such as TLS 1.0, TLS 1.1, and SSLv3. It's included to give you a little more detail about how protocol version rules work.
You should exclude nonsecure protocols from your network because they are all exploitable. In this example:
-
You can block some protocols using Version page on the decryption rule.
-
Because the system considers SSLv2 as undecryptable, you can block it using the Undecryptable Actions on the decryption policy.
-
Similarly, because compressed TLS/SSL is not supported, you should block it as well.
Important | Use the Cipher Suite and Version rule conditions only in rules with either the Block or Block with reset rule actions. Do not use Cipher Suite and Version with Decrypt - Resign or Decrypt - Known Key rule actions. These conditions in rules with other rule actions can interfere with the system's ClientHello processing, resulting in unpredictable performance. |
Procedure
Step 1 | Click . |
Step 2 | Click Edit ( |
Step 3 | Click Edit ( |
Step 4 | Click Add Rule. |
Step 5 | In the Add Rule dialog box, in the Name field, enter a name for the rule. |
Step 6 | From the Action list, click Block or Block with reset. |
Step 7 | Click Version page. |
Step 8 | Check the check boxes for protocols that are no longer secure, such as SSL v3.0, TLS 1.0, and TLS 1.1. Clear the check boxes for any protocols that are still considered secure. The following figure shows an example.
|
Step 9 | Choose other rule conditions as needed. |
Step 10 | Click Add. |