Troubleshoot TLS/SSL pinning
You can view connection events to determine whether or not the devices are experiencing TLS/SSL pinning. You must add at least the SSL Flow Flags and SSL Flow Messages columns to the table view of connection events.
Before you begin
-
Enable logging for your decryption rules as discussed in the section on logging decryptable connections in decryption rules in the Secure Firewall Management Center and Threat Defense Management Network Administration guide.
-
Log in to a mobile application like Facebook; if a network connection error displays, log in to Facebook using Chrome or Safari. If you can log in using a web browser but not the native application, TLS/SSL pinning is likely occurring.
Procedure
Step 1 | Click . |
Step 2 | Click Table View of Connection Events. |
Step 3 | Click x on any column in the connection events table to add additional columns for at least SSL Flow Flags and SSL Flow Messages.
The following example shows adding the SSL Actual Action, SSL Flow Error, SSL Flow Flags, SSL Flow Messages, SSL Policy, and SSL Rule columns to the table of connection events. 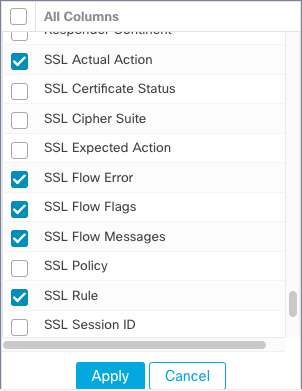 The columns are added in the order discussed in the section on connection and security intelligence event fields in the Secure Firewall Management Center and Threat Defense Management Network Administration guide. |
Step 4 | Click Apply. |
Step 5 | The following paragraphs discuss how you can identify SSL pinning behavior. |
Step 6 | If you determine that applications in your network use SSL pinning, see Decryption Rulesrule-based decryption rules guidelines and limitations. |
What to do next
You can use TLS/SSL connection events to confirm TLS/SSL pinning is occurring by looking for any of the following:
-
Applications that send an SSL ALERT Message as soon as the client receives the SERVER_HELLO, SERVER_CERTIFICATE, SERVER_HELLO_DONE message from the server, followed by a TCP Reset, exhibit the following symptoms. (The alert, Unknown CA (48), can be viewed using a packet capture.)
-
The SSL Flow Flags column displays ALERT_SEEN but not APP_DATA_C2S or APP_DATA_S2C.
-
If your managed device has SSL hardware acceleration enabled, the SSL Flow Messages column typically displays: CLIENT_ALERT, CLIENT_HELLO, SERVER_HELLO, SERVER_CERTIFICATE, SERVER_KEY_EXCHANGE, SERVER_HELLO_DONE.
-
If your managed device doesn't support SSL hardware acceleration or if the feature is disabled, the SSL Flow Messages column typically displays: CLIENT_HELLO, SERVER_HELLO, SERVER_CERTIFICATE, SERVER_KEY_EXCHANGE, SERVER_HELLO_DONE.
-
Success is displayed in the SSL Flow Error column.
-
-
Applications that send no alerts but instead send TCP Reset after the SSL handshake is finished exhibit the following symptoms:
-
The SSL Flow Flags column does not display ALERT_SEEN, APP_DATA_C2S, or APP_DATA_S2C.
-
If your managed device has SSL hardware acceleration enabled, the SSL Flow Messages column typically displays: CLIENT_HELLO, SERVER_HELLO, SERVER_CERTIFICATE, SERVER_KEY_EXCHANGE, SERVER_HELLO_DONE, CLIENT_KEY_EXCHANGE, CLIENT_CHANGE_CIPHER_SPEC, CLIENT_FINISHED, SERVER_CHANGE_CIPHER_SPEC, SERVER_FINISHED.
-
If your managed device doesn't support SSL hardware acceleration or if the feature is disabled, the SSL Flow Messages column typically displays: CLIENT_HELLO, SERVER_HELLO, SERVER_CERTIFICATE, SERVER_KEY_EXCHANGE, SERVER_HELLO_DONE, CLIENT_KEY_EXCHANGE, CLIENT_CHANGE_CIPHER_SPEC, CLIENT_FINISHED,SERVER_CHANGE_CIPHER_SPEC, SERVER_FINISHED.
-
Success is displayed in the SSL Flow Error column.
-
