Current identities for applications and operating systems
A current identity is an identity determination for an application or operating system that
-
represents the identity that the system finds most likely to be correct,
-
is used for vulnerability assignments and impact assessments, and
-
is determined by source priorities when multiple identities exist for the same host.
Current identity uses
The system uses the current identity for an operating system or application for these purposes:
-
Assign vulnerabilities to a host
-
Assess impact
-
Evaluate correlation rules relating to operating system identifications, host profile qualifications, and compliance allow lists
-
Display in the Hosts and Servers table views in workflows
-
Display in the host profile
-
Calculate the operating system and application statistics on the Discovery Statistics page
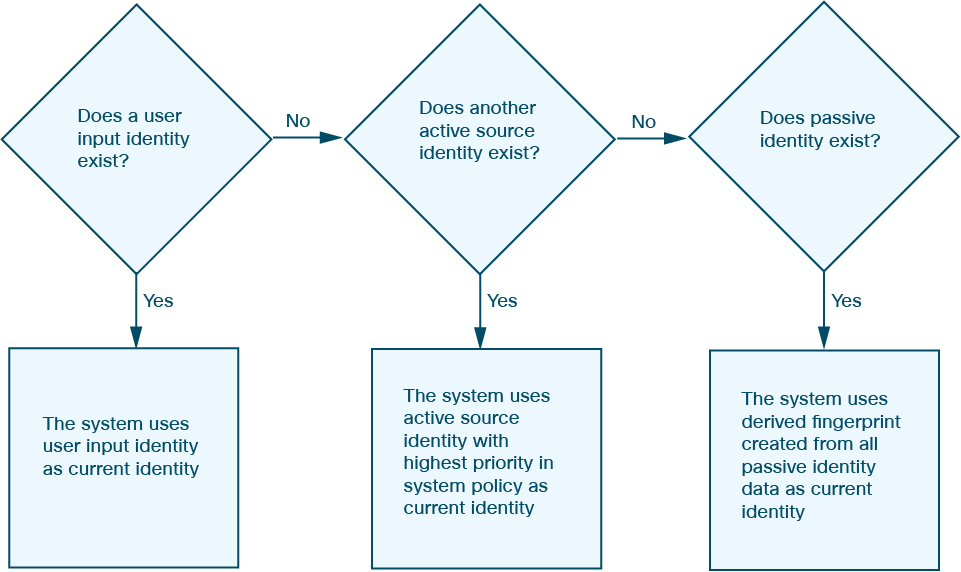
The system uses source priorities to determine which active identity should be used as the current identity for an application or operating system.
The database may retain information from multiple sources for an operating system or for a specific application on a host.
The system treats an operating system or application identity as the current identity when the source for the data has the highest source priority. Possible sources have this priority order:
-
User
-
Scanner and application (set in the Network Discovery Policy)
-
Managed devices
-
NetFlow records
If a new higher priority application identity has less detail than the current identity, it will not override the current application identity.
In addition, when an identity conflict occurs, the resolution of the conflict depends on settings in the network discovery policy or on your manual resolution.
Operating system assignment as current identity
For example, if a user sets the operating system to Windows 2003 Server on a host, Windows 2003 Server becomes the current identity and attacks targeting Windows 2003 Server vulnerabilities on that host are given a higher impact. The vulnerabilities listed for that host in the host profile include Windows 2003 Server vulnerabilities.