Decryption Policy Exclusions
This task discusses how to exclude certain types of traffic from decryption. We create Do Not Decrypt rules in your decryption policy for these although the rules are initially enabled only for an outbound decryption policy (that is, one that uses the Decrypt - Resign policy action).
Before you begin
You must upload an internal CA certificate for your managed device before you can create a decryption policy that protects outbound connections. You can do this in any of the following ways:
-
Create an internal CA certificate object by going to and referring to PKI.
-
At the time you create this decryption policy.
Procedure
Step 1 | Complete the tasks discussed in: | ||||||||
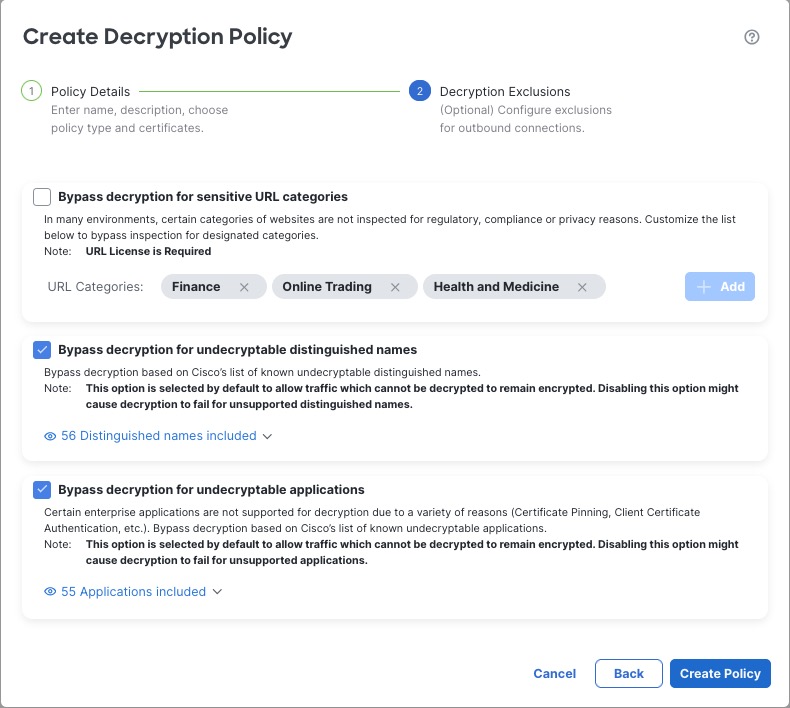
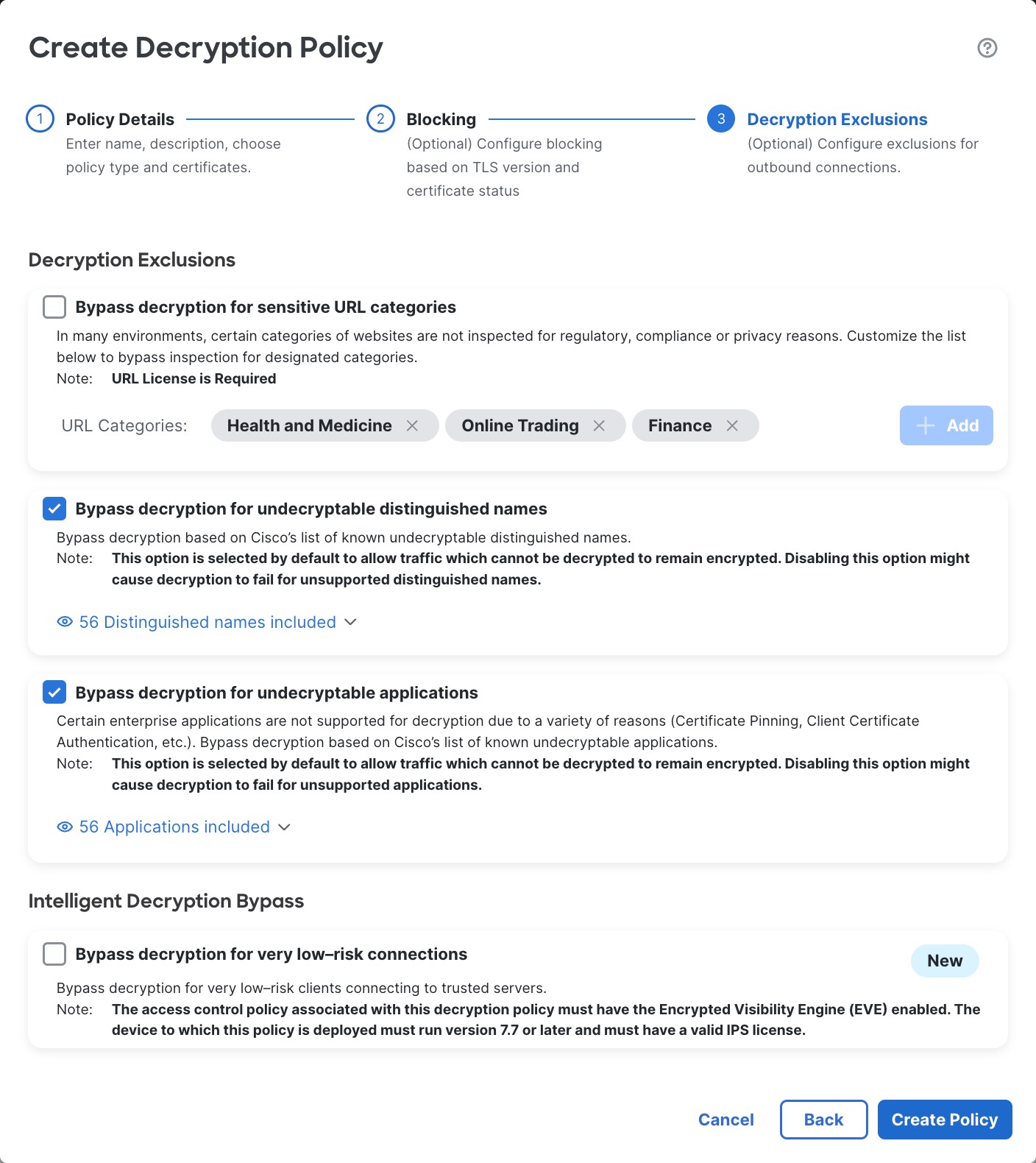
Step 2 | The exclusions page provides the following options. All options are enabled for an outbound protection policy (Decrypt - Resign rule action) and disabled for all other decryption policy actions.
The following figure shows the default options.
| ||||||||
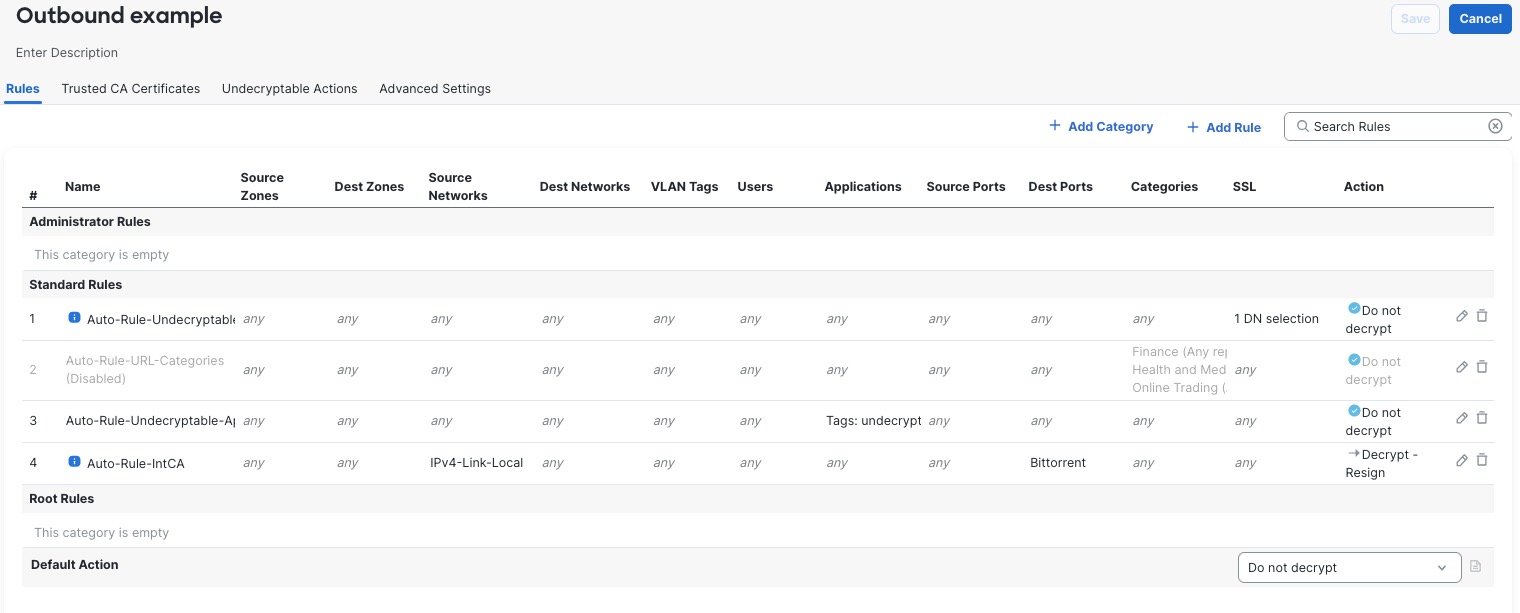
Step 3 | Click Create Policy. The following figure shows a sample outbound protection policy.
In the preceding example, the Do Not Decrypt rules corresponding to your choices for rule exclusions are automatically added before the Decrypt - Resign rule. The rule for sensitive URL categories is disabled because, by default, that exclusion is disabled. Had you selected the Bypass decryption for sensitive URL categories check box, the rule would have been enabled. | ||||||||
Step 4 | Click Create Policy. |
What to do next
-
Add rule conditions: Decryption Rule Conditions
-
Add a default policy action: Decryption Policy Default Actions
-
Configure logging options for the default action .
-
Set advanced policy properties: Decryption Policy Advanced Options.
-
Associate the decryption policy with an access control policy as described in Associating Other Policies with Access Control.
-
Deploy configuration changes.