Managing Cisco Secure Firewall Cloud Native using CDO
Cisco Defense Orchestrator (CDO) is a cloud-based, multi-device manager that provides a simple, consistent, and secure way of managing security policies on all your Secure Firewall Cloud Native devices.
The goal of this document is to provide customers new to Cisco Defense Orchestrator (CDO) with an outline of activities you can use to standardize objects and policies, upgrade managed devices, and manage VPN policies and monitor remote workers. This document assumes the following:
-
You have opened a 30-day trial account or you have purchased CDO and Cisco has created a CDO tenant for you.
-
You have setup a single-sign on account for your Super Admin user.
-
YourSecure Firewall Cloud Native are already configured and you are using them in your enterprise.
Following the outline of device orchestration activities, this document introduces CDO’s CLI interface, Change Log, public REST API, and provides summaries of some of the other features CDO can manage on your devices.
About Cisco Secure Firewall Cloud Native
The Cisco Secure Firewall Cloud Native seamlessly extends Cisco's industry-leading security to a cloud-native form factor (CNFW) using Kubernetes (K8s) orchestration to achieve scalability and manageability. Amazon Elastic Kubernetes Service (Amazon EKS) gives you the flexibility to start, run, and scale Kubernetes applications in the AWS cloud. Amazon EKS helps you provide highly-available and secure clusters and automates key tasks such as patching, node provisioning, and updates.
Cisco Defense Orchestrator (CDO) allows you to onboard and manage the Secure Firewall Cloud Native that has been created. It can be managed like any other virtual ASA device onboarded to CDO.
-
Onboard Secure Firewall Cloud Native. You can use the URL of the cluster and Kubernetes token to onboard the firewall.
-
Apply zero-day configuration to a Cisco Secure Firewall Cloud Native. When a Secure Firewall Cloud Native is created, it may not have a zero-day configuration. CDO allows you to onboard an uninitialized firewall and apply an initial configuration to it.
-
Manage firewall configuration. You can view, edit, and restore the configuration file of the firewall.
-
Read configuration changes. You can read the firewall's configuration file changes to CDO's database.
-
You can create and modify objects and use them in different policies that handle ingress and egress traffic of the firewall.
-
You can view, configure, and download IPv4 subnet pools on the firewall.
-
You can modify Remote Access VPN Configuration and connection profiles configured on the firewall. Note that you cannot upload new AnyConnect packages and AnyConnect client profiles to the firewall. You are also not allowed to create a new RA VPN configuration.
-
You can view real-time and historical data from active AnyConnect RA VPN sessions on the firewall.
-
Deploy configuration changes. You can deploy the changes you have made to the firewall.
-
Out-of-band change detection. When you enable Conflict Detection, CDO checks onboarded firewall for changes at a default time interval, which can be configured from the general settings page or overridden for a single device. If there is a change, the firewall's status will change to Conflict Detected, and you will be able to resolve the conflict either by accepting or rejecting the changes.
-
Change Log. The change log captures all the changes you make on the firewall, both using CDO and out-of-band.
Note | Some features are not supported on the firewall using CDO:
|
Supported Documents
Secure Device Connectors
Every tenant is initially provisioned with a cloud-based Secure Device Connectors and customers can install up to 4 additional on-premises SDCs in their own environments. The SDC enables your Secure Firewall Cloud Native to communicate with CDO.
Deploying more than one SDC for your tenant allows you to manage more devices with your CDO tenant without experiencing performance degradation. The number of devices a single SDC can manage depends on the features implemented on those devices and the size of their configuration files. For the purposes of planning your deployment, however, we expect one SDC to support approximately 500 devices.
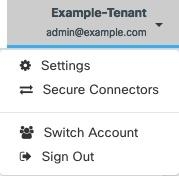
To view SDC:
-
Log in to CDO.
-
From the user menu, select Secure Connectors.
Create Additional CDO Users on your Tenant
There are a variety of user roles in Cisco Defense Orchestrator (CDO): Read-Only, Edit-Only, Deploy-only, Admin, and Super Admin. User roles are configured for each user on each tenant. If a CDO user has access to more than one tenant, they may have the same user ID but different roles on different tenants. When the interface or the documentation refers to a Read-only user, an Admin user, or a Super Admin user we are describing that user's permission level on a particular tenant. See Create a User Record for a User Role to learn about the privileges granted to different types of users.
When your tenant was created, you were automatically assigned a Super Admin user. The Super Admin has the ability to create other users on your tenant. For those new users to connect to the tenant, they need to have, or create, a Cisco Secure Sign-On account with the same email address as their user record in CDO. See Create a User Record for a User Role to create a user record in CDO.
Policy Orchestration
Policy orchestration involves reviewing objects and policies. Keep in mind when you are working with Secure Firewall Cloud Native policies that CDO refers to Secure Firewall Cloud Native "access-groups" as "access policies." When you look for Secure Firewall Cloud Native access policies you navigate from the CDO menu bar Policies > ASA Access Policies.
Resolve Network Object Issues
Over the years, you may have objects on your security device that are no longer used, are duplicates of other objects, or whose values are inconsistent across devices. Begin your orchestration task by fixing these object issues.

Address object issues in a the order below. The work you do in the early steps may resolve the number of issues you have to address in later steps:
-
Unused Objects
 . CDO identifies network policy objects that exist in a device configuration but are not referenced by another object, an access-list, or a NAT rule. Find these unused objects and delete them.
. CDO identifies network policy objects that exist in a device configuration but are not referenced by another object, an access-list, or a NAT rule. Find these unused objects and delete them. -
Duplicate Objects
 . Duplicate objects are two or more objects on the same device with different names but the same values. These objects are usually created accidentally, serve similar purposes, and are used by different policies. Look for opportunities to standardize names while recognizing that some duplicates may exist for legitimate reasons.
. Duplicate objects are two or more objects on the same device with different names but the same values. These objects are usually created accidentally, serve similar purposes, and are used by different policies. Look for opportunities to standardize names while recognizing that some duplicates may exist for legitimate reasons. -
Inconsistent Objects
 . Inconsistent objects are objects on two or more devices with the same name but different values. Sometimes users create objects in different configurations with same name and content but over time the values of these objects diverge which creates the inconsistency. Consider standardizing the values in these objects or renaming one to identify it as a different object.
. Inconsistent objects are objects on two or more devices with the same name but different values. Sometimes users create objects in different configurations with same name and content but over time the values of these objects diverge which creates the inconsistency. Consider standardizing the values in these objects or renaming one to identify it as a different object.
Fix Shadow Rules
Now that you have resolved your network object issues, review network policies for shadow rules and fix them. A shadow rule is marked by a half-moon badge  on the network policies page. It is a rule in a policy that will never trigger because a rule with higher priority in the policy acts on all the packets before they reach the shadowed rule. If there is a shadowed rule that will never be hit, remove it, or edit the policy to bring that rule "into the light."
on the network policies page. It is a rule in a policy that will never trigger because a rule with higher priority in the policy acts on all the packets before they reach the shadowed rule. If there is a shadowed rule that will never be hit, remove it, or edit the policy to bring that rule "into the light."
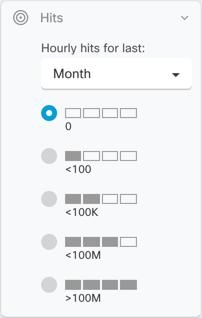
Evaluate Policy Hit Rates
Are your policies evaluating network traffic? CDO gathers hit rate data on your policies every hour. The longer your devices are managed by CDO the more meaningful the hit rate data on a particular policy will be. Filter network policies by device and hit count to learn if a policy is effective. If it is not, consider rewriting it or deleting it.
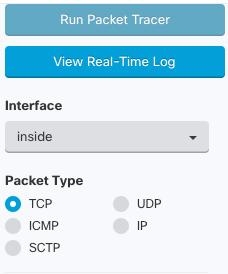
Troubleshoot Policies
Use ASA packet tracer to test the path of a synthetic packet through a policy and determine if a rule is inadvertently blocking or allowing access.
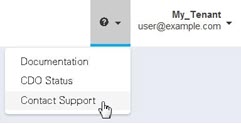
Search the CDO documentation for troubleshooting topics. We've tagged many topics as troubleshooting topics to help you find them easily. If you don't see the one you need, let us know by contacting Cisco TAC from the Contact Support page.
Monitor and Manage VPN Connections
Review Site-to-Site VPN Issues
CDO reports VPN issues present on your Secure Firewall Cloud Native devices in your network. You can look at your environment two ways, as a table showing a listing of VPN peers or a map showing your VPN connections in a hub and spoke topology. Use the filter sidebar to search of VPN tunnels that need your attention.
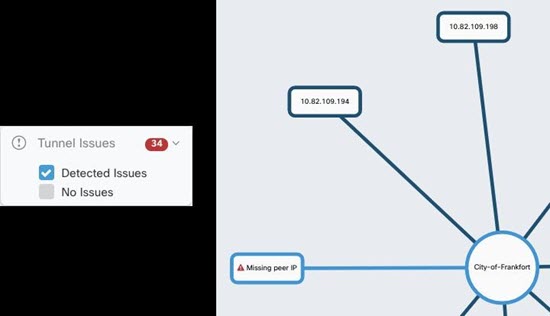
Use CDO to evaluate your VPN tunnels:
-
Check Site-to-Site VPN Tunnel Connectivity
-
Find VPN Tunnels with Missing Peers
-
Find VPN Peers with Encryption Key Issues
-
Find Incomplete or Misconfigured Access Lists Defined for a Tunnel
-
Find Issues in Tunnel Configuration
ASA Remote Access VPN Support
CDO allows creating remote access virtual private network (RA VPN) configurations to allow users to securely access enterprise resources when connecting through the Secure Firewall Cloud Native. When your Secure Firewall Cloud Native are onboarded to CDO, CDO recognizes any RA VPN settings that have already been configured using ASDM or Cisco Security Manager (CSM) and you will be able to manage them with CDO.
AnyConnect is the only client that is supported on endpoint devices for RA VPN connectivity.
CDO supports the following aspects of RA VPN functionality on Secure Firewall Cloud Native devices:
-
SSL client-based remote access
-
IPv4 and IPv6 addressing
-
Shared RA VPN configuration across multiple Secure Firewall Cloud Native devices
Monitor Device Configuration Synchronization
CDO periodically compares the device configuration it has stored in its database with the one installed on the Secure Firewall Cloud Native. An onboarded Secure Firewall Cloud Native can still be managed by the device's Adaptive Security Device Manager (ASDM), so CDO makes sure that the configuration it has is the same as the configuration on the device and alerts you to differences. See Conflict Detection for more information about the Synced, Not Synced or Conflict Detected device states.
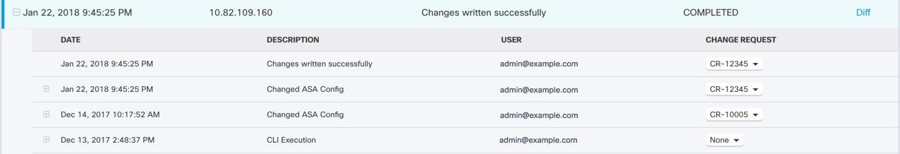
Keep Track of Changes in the Change Log
The changes you make to your device's configurations are recorded in the Change Logs. The change log displays information like changes deployed from CDO to your device, changes imported from your device to CDO, what the change was along with the ability to see a "diff" of that change, when it happened, and who did it.
You can also create and apply a custom label, that uses your company's tracking number, to the changes you make. In the change log, you can filter the list of changes by that custom label, a date range, by a specific user, or by change type to find what you're looking for.
Restore a Previous Configuration
If you make changes to an Secure Firewall Cloud Native that you want to "undo," you can use CDO to restore the device to a previous configuration.
Managing Devices Using a Command Line Interface and Command Macros
CDO is a web-based management product that provides you with both a graphic user interface (GUI) and a command line interface (CLI) to manage your devices one at a time or many at once.
Secure Firewall Cloud Native CLI users will appreciate the extra capabilities of our CLI tool. Here are some of the reasons to use CDO's CLI tool rather than connecting to the device with an SSH session:
-
CDO knows what user mode is needed for a command. You do not need to elevate or lower your permission level to execute a command, nor do you need to enter the specific command context to execute a command.
-
CDO retains command history, so you can easily re-run a command by picking it from a list.
-
CLI actions are logged in the change log, so you can read what command was sent and what action was taken.
-
Commands can be run in bulk mode, allowing you to deploy objects or policies to multiple devices simultaneously.
-
CDO supplies CLI macros. CLI macros are stored ready-to-use commands you can run as they are, or "fill-in-the-blank" CLI commands you can complete and run. You can run these commands on one device or send the command to multiple Secure Firewall Cloud Native at the same time.
-
CLI provides you with the complete Secure Firewall Cloud Native configuration file. You can view it or, if you are an advanced user, edit it directly and save your changes rather than issuing CLI commands to change it.
CDO Public API
CDO has published its public API and provided you with documentation, examples, and a playground to try things out. The goal of our public API is to provide you with a simple and effective way to perform a lot of what you would normally be able to do in the CDO UI, but in code.
To use this API, you will need to know GraphQL. It is very easy to learn, and their official guide (https://graphql.org/learn/) provides a thorough, light read. We chose GraphQL because it is flexible, strongly typed, and auto-documenting.
To find the full schema documentation, simply go to the GraphQL Playground, and click on the docs tab on the right hand side of the page.
You can launch the CDO Public API from this link or by selecting </>CDO API from the user menu.
Integrate CDO with SecureX
The Cisco SecureX platform connects the breadth of Cisco’s integrated security portfolio and the customer’s infrastructure for a consistent experience that unifies visibility, enables automation, and strengthens your security across network, endpoint, cloud, and applications. By connecting technology in an integrated platform, SecureX delivers measurable insights, desirable outcomes, and unparalleled cross-team collaboration. You can read more about SecureX and CDO and how to Add CDO to SecureX.
What to do Next
Now you can begin onboarding your Secure Firewall Cloud Natives and orchestrating your policies.
If You Need Help
You can contact support, ask a question, or read our product documentation by clicking on our support menu in the CDO GUI.