Create an identity policy and active authentication rule
This procedure enables captive portal to perform active authentication for users in your domains using the Secure Firewall Management Center.
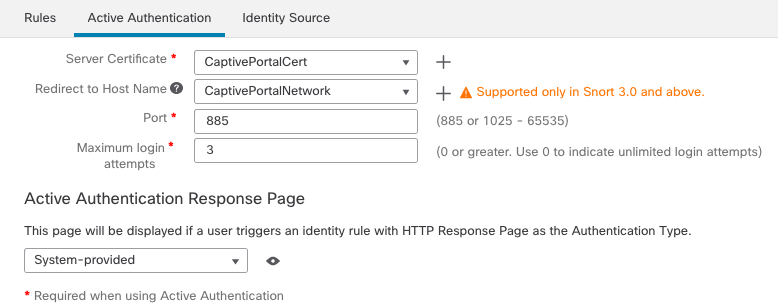
This multi-part procedure shows how to set up the captive portal using the default TCP port 885 and using a Cloud-Delivered Firewall Management Center server certificate for both the captive portal and for TLS/SSL decryption. Each part of this example explains one task required to enable the captive portal to perform active authentication.
If you follow all the steps in this procedure, you can configure captive portal to work for users in your domains. You can optionally perform additional tasks, which are discussed in each part of the procedure.
For an overview of the entire procedure, see Configure the captive portal for user control.
Procedure
Step 1 | In the Firewall Management Center, click and create or edit an identity policy. |
Step 2 | (Optional.) Click Add Category to add a category for the captive portal identity rules and enter a Name for the category. |
Step 3 | Click the Active Authentication tab. |
Step 4 | Click Save. |
Step 5 | Click the Rules tab. |
Step 6 | Click Add Rule to add a new captive portal identity policy rule, or click Edit ( In the Add Rule page, |
Step 7 | At the top of the page, click Save. |
What to do next
Continue with Create a TCP port access control rule.