flowbits Keyword Example: A Configuration Resulting in False Positive Events
Including different state names that are set in different rules in a group can prevent false positive events that might otherwise occur when content in a subsequent packet matches a rule whose state is no longer valid. The following example illustrates how you can get false positives when you do not include multiple state names in a group.
Consider the case where the following three rule fragments trigger in the order shown during a single session:
(msg:"JPEG transfer"; content:"image/";pcre:"/^Content-?Type\x3a(\s*|\s*\r?\n\s+)image\x2fp?jpe?g/smi";
?flowbits:set,http.jpeg; flowbits:noalert;)
The following diagram illustrates the effect of the
flowbits keyword in the preceding rule fragment:
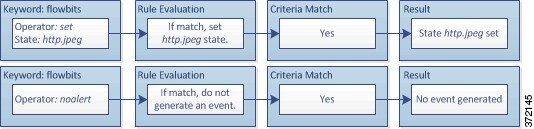
The
content and
pcre keywords in the first rule fragment match a JPEG
file download,
flowbits:set,http.jpeg sets the
http.jpeg flowbits state, and
flowbits:noalert stops the rule from generating events.
No event is generated because the rule’s purpose is to detect the file download
and set the
flowbits state so one or more companion rules can test
for the state name in combination with malicious content and generate events
when malicious content is detected.
The next rule fragment detects a GIF file download subsequent to the JPEG file download above:
(msg:"GIF transfer"; content:"image/"; pcre:"/^Content-?Type\x3a(\s*|\s*\r?\n\s+)image\x2fgif/smi";
?flowbits:set,http.jpg,image_downloads; flowbits:noalert;)
The following diagram illustrates the effect of the
flowbits keyword in the preceding rule fragment:
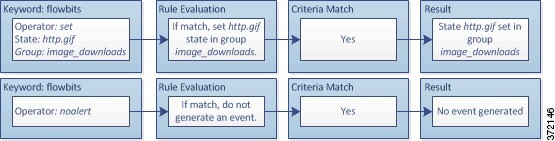
The
content and
pcre keywords in the second rule match the GIF file
download,
flowbits:set,http.jpg sets the
http.jpg flowbit state, and
flowbits:noalert stops the rule from generating an
event. Note that the
http.jpeg state set by the first rule fragment is still
set even though it is no longer needed; this is because the JPEG download must
have ended if a subsequent GIF download has been detected.
The third rule fragment is a companion to the first rule fragment:
(msg:"JPEG exploit";?flowbits:isset,http.jpeg;content:"|FF|";
pcre:"?/\xFF[\xE1\xE2\xED\xFE]\x00[\x00\x01]/";)
The following diagram illustrates the effect of the
flowbits keyword in the preceding rule fragment:

In the third rule fragment,
flowbits:isset,http.jpeg determines that the
now-irrelevant
http.jpeg state is set, and
content and
pcre match content that would be malicious in a JPEG
file but not in a GIF file. The third rule fragment results in a false positive
event for a nonexistent exploit in a JPEG file.